He is every compliance or IT security officer’s nightmare: the trainee. What may seem surprising at first glance is, unfortunately, often standard practice and reveals a serious security vulnerability. As a trainee moves through the company’s departments, he is typically granted access rights upon access rights so that he can perform the necessary tasks in each team. The problem: Instead of having these privileges revoked afterward, they keep them, gradually accumulating more and more permissions. In the worst-case scenario, by the end of their training, they have more access rights than the IT director, even though they don’t need them at all. Often, only the CEO has more access rights—a highly dangerous situation for any company.
Access for All – The Consequences
Whether an intern or a CEO—as a rule, no employee needs access to all of the company’s data. It’s concerning enough if a trainee can accidentally view and delete payroll documents. But overly broad access rights at the executive level pose entirely different risks. Logically, the most sought-after targets for cybercriminals are those who hold the highest positions in companies—after all, it’s assumed that they have unrestricted access to the most critical data. This is not an entirely unfounded assumption, as managing directors in particular still hold the view that, as bosses, they must have access to everything. To learn why this is absolutely unnecessary and does more harm than good, please also read our specialized article on the subject.
Uncontrolled and unchecked access permissions across all departments and levels of a company are generally not recommended and can have serious consequences:
1. Increased risk of insider threats
Employees or applications with excessive privileges can cause significant or even catastrophic damage, either unintentionally or intentionally.
2. Greater impact in the event of security breaches
If attackers gain access to privileged accounts, they can cause significant damage by accessing critical systems and data. This can lead to data theft, espionage, or extortion attempts through encryption, all of which can cause massive harm to companies.
3. Non-compliance with legal requirements
Companies risk heavy fines and reputational damage if they fail to comply with data protection and security requirements.
As much as necessary, as little as possible—the principle of least privilege
The principle of least privilege (LPP) is a fundamental security concept in IT that aims to grant each user or application only the rights and access privileges necessary to perform their tasks—as much as necessary and as little as possible. The goal, therefore, is to strictly limit access to data and systems and allow only what is absolutely necessary. This significantly reduces the risk that errors or malicious activities could cause significant damage.
Why is the principle of least privilege so important?
Cyberattacks and insider threats pose a growing risk to businesses. Their biggest challenge is protecting their IT infrastructure while remaining flexible and efficient. If access rights are not restricted, the attack surface expands—much like a door left wide open to the company. The least privilege principle minimizes the impact of potential security incidents and is therefore an indispensable component of a comprehensive IT security strategy.
Implementation strategies for the principle of least privilege
But how can this much-touted principle be put into practice? What is the best approach, and what needs to be taken into account? As a general rule, implementation options and requirements vary from company to company and depend heavily on the company’s size and IT infrastructure. Accordingly, different approaches can be taken. The following strategies have proven effective:
1. Role-Based Access Control (RBAC)
With RBAC, access to systems and data is granted based on a user’s role within the company. For example, accounting staff have access only to financial systems, while IT staff have access to technical systems.
2. Multi-factor authentication (MFA)
MFA requires users to verify their identity using multiple methods before they are granted access to systems. This reduces the risk of unauthorized access, even if login credentials have been compromised.
3. Regular review and adjustment of access rights
Companies should regularly review users' access rights and ensure that they only have access to the resources they actually need. Unnecessary access rights should be removed.
4. Logging and Monitoring
Continuous monitoring and logging of access attempts make it possible to quickly detect and respond to unusual activity. This allows potential security breaches to be detected early on.
Administrator Rights in IT Support – F4SD and the Principle of Least Privilege
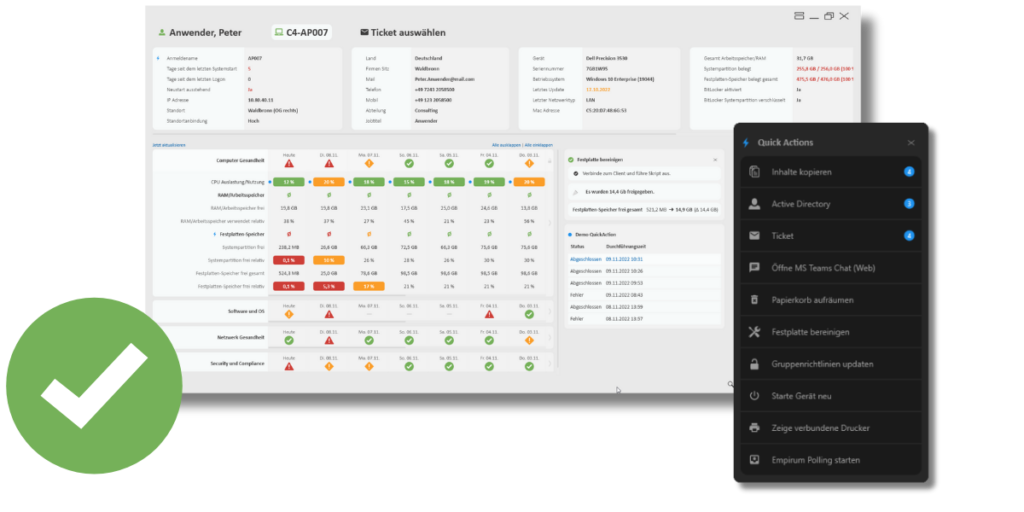
IT support staff, in particular, often require extensive access rights to collect and analyze data and troubleshoot issues. Whether it’s remote access to users’ computers or access to relevant client data, support staff often need extensive administrative privileges just to do their jobs. However, when the service desk uses F4SD, many of these access permissions become obsolete.
Instead of a human, the F4SD agent collects relevant data from clients and presents it clearly in the application’s dashboard. As a result, IT support staff no longer need extensive access or administrative privileges. Furthermore, the integration of PowerShell-based Quick Actions enables automated execution of actions directly from within the tool, which also reduces the need for permissions outside the tool. Overall, F4SD not only contributes to standardizing service desk workflows but also supports the practical implementation of the least privilege principle.
Conclusion – Take Away the Boss's Powers
Whether it’s a trainee or a CEO—both examples clearly illustrate the risks that can arise from uncontrolled access rights within a company. The principle of least privilege is an important security measure that allows access by individuals—even that of a CEO—to be restricted to what is strictly necessary. With tools likeF4SD, this principle can be effectively implemented without compromising efficiency—a smart approach to strengthening IT security in everyday operations.